Last changed: 15.03.2020
Wardriving
To prepare a wireless penetration test you should begin with identifying the networks which are in scope. This can be done by recording all found beacons on site and mark them with their gps position. This way you can plot all found networks in a map and see which ones belong to the targeted area. Referring to the process of wardialing this procedure is called wardriving.
Aside from driving around with a notebook, smaller sites could be surveyed by
warwalking with a small device like the Nokia N900 which works with
its internal gps receiver.
In this article I will outline some basic steps and tools needed for wardriving
in kali linux.
setup the gps device
If you are using an usp gps device it should get detected by linux and be
configured as a serial device like /dev/ttyUSB0. To find the correct name
check dmesg after connecting the device.
If kismet is the only tool which reads out data from the gps device you can
configure the serial device directly. Change the gps configuration in
/etc/kismet/kismet.conf according to this.
/etc/kismet/kismet.conf
...
gps=true
gpstype=serial
gpsdevice=/dev/ttyUSB0
...In case you are planning to use the gps data with multiple tools at once you
should use the gps daemon gpsd and let every other tool connect to the socket
gpsd opens.
To check if gpsd is working correctly I recommend the tool gpsmon.
gpsd -n /dev/ttyUSB0The use of gpsd has to be configured in the file /etc/kismet/kismet.conf
as follows.
/etc/kismet/kismet.conf
...
gps=true
gpstype=gpsd
gpshost=localhost:2947
...wardriving with kismet
If the gps device is receiving valid positioning data and the configuration in
/etc/kismet/kismet.conf is adjusted to use the correct device kismet can be
started to record data. The current position will be displayed if GPS Data is
activated in the View tab of kismet.
In the packet capture of kismet there will be an additional PPI header in
every recorded packet which contains the corresponding gps position.
store network data in a sqlite database using vikismet
The advantage of storing a summary of the recorded data in an additional database is the ability to easily handle the aggregated results of multiple wardriving sessions. For this purpose I customized the tool vikismet which is an improved version of GISKismet optimized for the tool viking.
vikismet -x kismet_file.netxml -d my_database
vikismet -q "select * from wireless" -d my_database -o export.gpxdisplay found networks in a map with viking
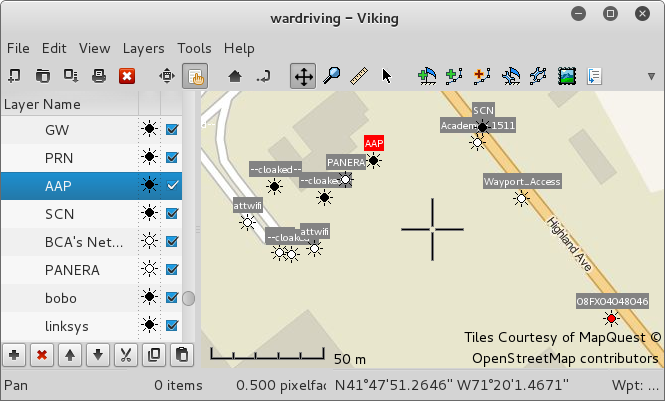
Most linux repositories contain the gtk tool viking which can be used to manage gps data and display it in OSM, Bing Aerial and other maps. The map data can be cached to use the tool offline.
Viking can open the gpx file generated by vikismet. A screenshot of viking can be seen at the top.
viking export.gpx